Contact us
Never let your business down
Distort Ransomware Perception
Use the Deceptive Bytes Platform to turn ransomware’s evasive tactics against itself, significantly reducing the attack surface and preventing the attack before it can even begin
Our valued customers
Trusted by organizations worldwide
Your Proactive defense against ransomware
19
Ransomware attacks per second
<2 sec
Prevented in less than
Over
1,000
Evasion techniques
Unique evasion techniques anticipated and countered
$4.54M
Average
Price per successful attack
>99.9%
Prevention Rate
Using malware defenses insures high prevention rate
<1.5mb
Disk Space
Free of threats database means no unnecessary disk space is used
We will take care of the attack, so you can take care of your business
Discover how thinking differently about ransomware protection can give your organization the edge it needs in the ongoing cyber warfare.
Prevention-first security
Focus on preventing unknown ransomware attacks (by unknown actors) before they execute, reducing alert fatigue and improving response times. Deceptive Bytes preemptive technology can reduce up to 90% of alerts sent to SIEM and other systems.
Proactive & Dynamic
Real-time adjustments of deception tactics distort ransomware’s perception of the attack surface, making it appear hostile or unworthy, hindering adversary reconnaissance efforts, and preventing ransomware execution.
Enhance resilience
Traditional tools like NGAVs and EDRs rely on detecting known threats. Deceptive Bytes’ preemptive approach, neutralizing threats before they can execute. By diverting attackers and uncovering stealthy cyberattacks early, Deceptive Bytes complements your existing security stack, enhancing your overall defense posture.
Reduce false-positives
Counteracting malware evasion techniques, Deceptive Bytes generates high-fidelity alerts. Forcing threats to reveal themselves during their reconnaissance phase, significantly reducing human error, dwell time, and false positive alerts compared to traditional solutions.
Lightweight & User-mode platform
Deceptive Bytes operates in user-mode, requiring minimal system resources. Its self-managed nature eliminates the need for reboots or in-memory footprints, ensuring seamless operations and minimal operational overhead for security team.

Scalability and Integration
Operating alongside and integrating with existing security infrastructure like EDR, EPP, and XDR systems, Deceptive Bytes fortifies organnizations defense strategy without disrupting IT environment.
Testimonials that Speak Volumes
Awards & Recognitions




Latest from Our Blog
Learn what's new with us and in cyber security
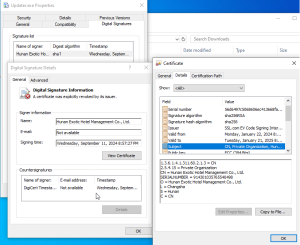
Case study – preventing Malgent trojan horse
12/09/2024
Intro Yesterday (September 12th, 2024) our Active Endpoint Deception platform prevented a new variant of Malgent trojan horse that was built just a few hours prior to the attack on…

The Role of Large Language Models in Enhancing Ransomware and Malware Threats
22/08/2024
As technology evolves, so do the tactics of cybercriminals. Large Language Models (LLMs) like GPT-4, designed to assist in various legitimate tasks, are being increasingly exploited by threat actors to…

Nation State Threat Actors in Cybersecurity: A Global Overview
10/07/2024
In today’s interconnected world, nation state threat actors represent some of the most sophisticated and persistent dangers in the realm of cybersecurity. These actors often leverage advanced persistent threats (APTs)…